Directory
Overview
As enterprises evolve around cloud based applications, Active Directory (AD) and Lightweight Directory Access Protocol (LDAP) plays a demanding role for the management of information security, computers and users. This documentation describes how mID Provider(IAM) platform securely interconnects with your Active Directory infrastructure and applications.
Benefits of Directory Integration
There are many benefits to integrate directory besides providing users to login to applications with existing credentials:
• Eliminating passwords - The combination of SAML SSO and mID Provider(IAM)'s AD integration excludes the use of passwords for client applications that is enabled with SAML protocol. Less passwords meaning reduced IT workload and improved security.
• Merge multiple directories - mID Provider(IAM) platform can merge and represent multiple directories as a single unified directory to client applications for federation.
• Avoid end-to-end app integrations - Client applications can delegate authentication process to directory via LDAP. However, when using many client applications, the cost of integration and maintenance increases.
• Central access control - Rather than logging into client applications directly, users can authenticate via trusted IdP, subject to MFAs.
• Central audit trail - Sign in activities can be reported in a central audit trail which facilitates cross application analysis and compliance.
LDAP Connector
This section provides more details about how KOBIL LDAP connector integrates with an AD.
Installation
Pre-Requisites
Hardware Requirements
- Intel Pentium Core 2 Duo 2.5 GHz (if virtualized, please make sure to have 2 virtual CPU cores available)
- 4 GB RAM (or more for large data volumes)
- Additionally 4 GB free hard disk space for the installation
Software Requirements
- KOBIL SSMS Server Version 2.9.x or newer, see release notes (on premise or cloud instance)
- LDAP- or Active Directory Server (optional):
- OpenLDAP
- Microsoft Active Directory based on
- Windows Server 2008 R2 or Windows 2012 Server
- OpenDJ should work as well, but is currently not tested.
- Internet Explorer
- Mozilla Firefox
- Google Chrome
System Environment and Tools
- Java Virtual Machine (JVM) 8 runtime. Please use Oracle JRE.
- Tomcat 8.0.x or 9.0.x (do not use 8.5.x!) Tests were done using 8.0.52, 9.0.8 & 9.0.12
- Operating Systems
- Linux 64 bit; e.g. RedHat Enterprise 7.4
- Windows Server 2008 R2
- Windows Server 2012 R2
Deployment
On-premise
Classical on premise deployment includes all server components, e.g. KOBIL SSMS server and KOBIL LDAP connector (LDAPc) are installed in the corporate IT network. In this case, the corporate firewall does not need to be further opened than required by SSMS server in order to run LDAPc. End user self-service enrollment is done fully in house.
Cloud-based
Cloud-based deployment allows a lightweight installation only of KOBIL LDAP connector (LDAPc) in the corporate IT network. The KOBIL SSMS server might be used in the cloud, so the corporate firewall just passes SSL/TLS-encrypted SOAP calls, protected by a public trusted SSL/TLS certificate. End user self-service enrollment is done fully in house. Cloud-based deployment is currently recommended for testing and pilot phases.
Configuration
Once you are done with LDAP Settings, click on “Next” to get to the SSMS settings screen where you can configure the connection to your SSMS server instance. LDAPc uses this access to SSMS server to create new users from LDAP synchronization and create activation codes for end user self-service app enrolment.
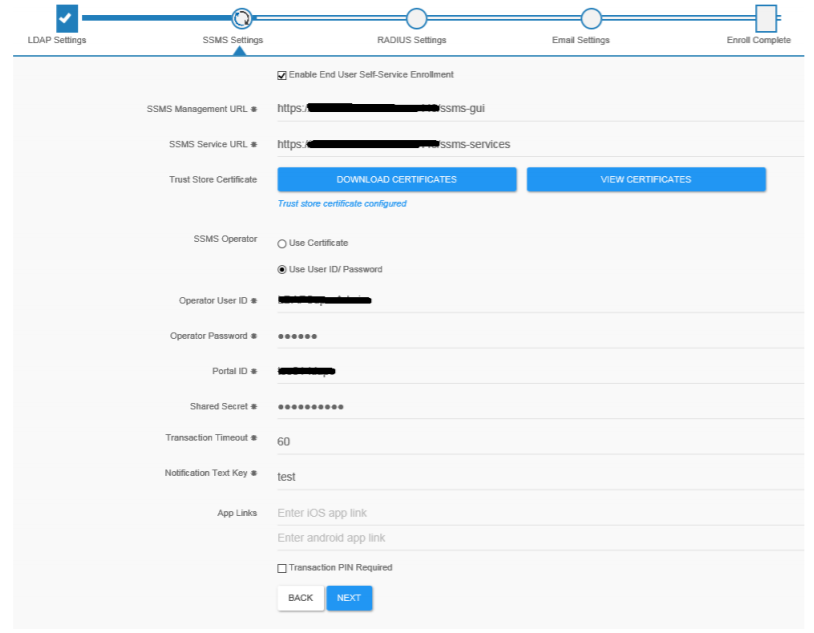
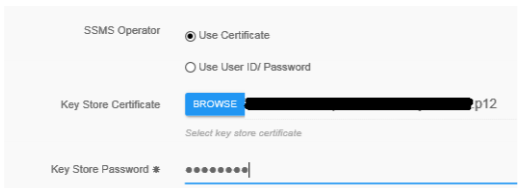
Along with editing the GUI settings, the Settings.xml can be manually edited using a text editor. The below table explains the property listing for SSMS.
| UI Setting | corresponding XML tag in settings.xml | Description |
|---|---|---|
| Enable End User Self-Service Enrollment | selfServiceEnrollment | If checked, this instance of LDAPc acts as a web instance. Requires “Use LDAP Server” to be enabled in LDAP settings! |
| SSMS Management URL | ssmsMgtURL | SSMS server management URL:https://your.ssms.url/ssms-gui You will obtain this URL from your SSMS administrator |
| SSMS Service URL | ssmsServicesURL | SSMS server services URL:https://your.ssms.url/ssms-services You will obtain this URL from your SSMS administrator |
| Download Certificate & View Certificate | trustStorePath /trustStorePassword | The trust store full file path location. This is automatically generated after downloading the SSMS server certificates via the UI. |
| Portal ID & Shared Secret | portalID /sharedSecret | The portal ID and the corresponding shared secret are configured in SSMS Kernel -> Administration -> PortalServices. |
| Transaction Timeout | transactionTimeout | Specifies the timeout for which the LDAP RADIUS connector will keep the transaction alive. After the specified timeout it will reject the SSMS login |
| Notification Text Key | notificationTextKey | The notification text resources key which is used during login transaction. This is a pointer to the SSMS Text Resource. For more information on the Text Resources, please consult the SSMS Kernel Administration |
| App Links | androidAppLink,iOSAppLink | The app link respective to Android and iOS platforms. If no links are specified, user will be redirected to default app store links from activation view. |
| Transaction PIN Required | transactionPinRequired | Set this flag to true if a PIN confirmation is required in |
| the client app | ||
| N/A | lockSSMSEnroll | If set to “true”, the SSMS enroll UI cannot be edited. Use this to pre-configure LDAPc and avoid unintended changes. Default value: “false” |
Required SSMS permissions
If you are using predefined roles in SSMS, at least the role “ADMIN” is required. In case of finer-grained roles, the following permissions have to be granted to the operator certificate:
- ASM_DEVICE_VIEW, ASM_DEVICE_MANAGE, ASM_USER_MODIFY, ASM_USER_VIEW, ASM_USER_ACTIVATION_CODE_VIEW, ASM_USER_ACTIVATION_CODE_MODIFY
- SSMS_USER_MANAGE, SSMS_USER_VIEW, SSMS_VIEW
- DB_TEXT_RESOURCE_VIEW
Required SSMS settings
In SSMS Web GUI / ASM module, please set the transaction timeout to 60 seconds so both the LDAP RADIUS interface and SSMS have matching configuration.
SSMS Extended REST API for Secure Communication Platform (SCP)
LDAPc supports an extended operation mode to support the extended SSMS REST API introduced for the KOBIL Secure Communication Platform (SCP). This requires an SCP infrastructure and is not available with the standard KOBIL SSMS server for the mAST product.
The extended REST API is activated by enabling the checkbox “Copy LDAP attributes to SSMS extended REST API / SCP” in the LDAP settings view (see section 4.1). By default, you should leave this setting disabled / unchecked. Only enable it if you are using a KOBIL SCP infrastructure. You can define which LDAP attributes are mapped in addition to the userID to the SSMS and SCP Address Book servers.
The current version of the SCP infrastructure / Address Book requires at least those attribute mappings shown in below screenshot. Whenever you make changes to the attribute mappings, please restart sync (see 4.1.2).
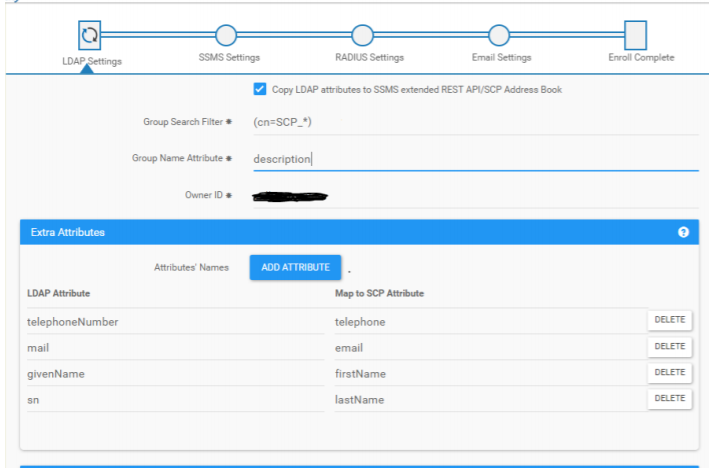
| UI Setting | corresponding XML tag in settings.xml | Description |
|---|---|---|
| Copy LDAP attributes to SSMS extended REST API/SCP address book | restEnabled | Enable this for mPower / SCP usage |
| Group Search Filter | groupSearchFilter | Defines the search filter to detect groups to synchronize. See below for details how groups are synchronized. A meaningful value would be “(cn=SCP_*)” but of course, this can be narrowed down more to be more specific on groups. |
| Group Name Attribute | groupNameAttribute | Which LDAP attribute should be taken to define the group’s “visible” name in ABS, especially for chat Groups as they are shown in the end user’s contact lists. Use for example “description” here. |
| OwnerID | ownerId | This is used to distinguish LDAPc instanced, especially if more than one connector is used to populate the ABS. Each instance of LDAPc (or other connectors) must get a unique ownerId. The ABS entry generated by an LDAPc instance is marked with this ownerId, and updates are only applied for matching ownerIds. |
| Extra Attributes(LDAP/SCP Mapping) | extraAttributes(key/Value) | Maps LDAP attributes to ABS attributes. By default you should at least create mappings for the ABS attributes “firstName”,“lastName”. Optionally, you can also define mappings for “email”, “telephone” and “contactPictureJPG” |