Login Brute Force
Login Brute Force Security Features
Login Brute Force is a security feature designed to prevent unauthorized access by detecting and blocking repeated attempts to guess a user’s password. If the number of failed login attempts exceeds a specified threshold, it can temporarily or permanently disable the user account.
How to configure
To configure Login BruteForce protection, follow these steps
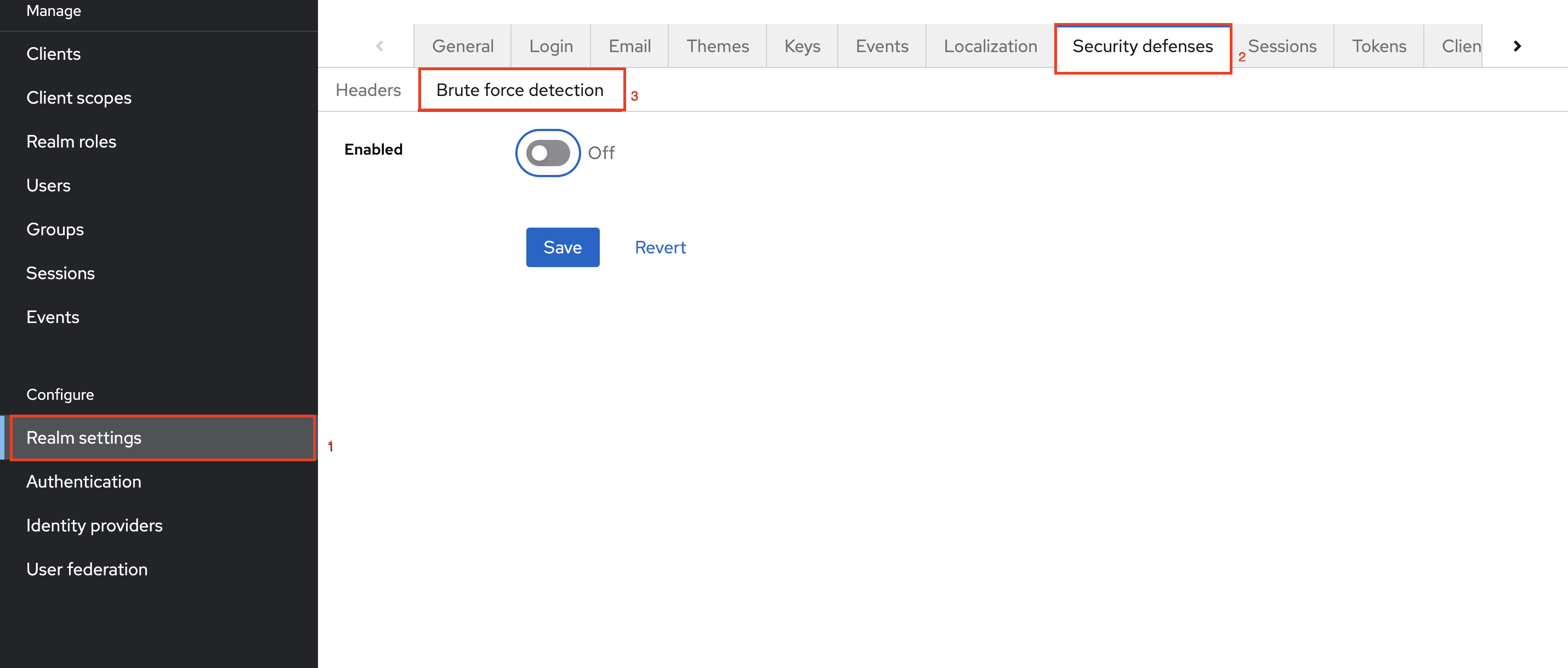
Step 1: Navigate to Realm settings
Step 2: Click on Security defenses tab.
Step 3: Under the Brute force detection tab.
Step 4: Toggle the option to On to activate protection.
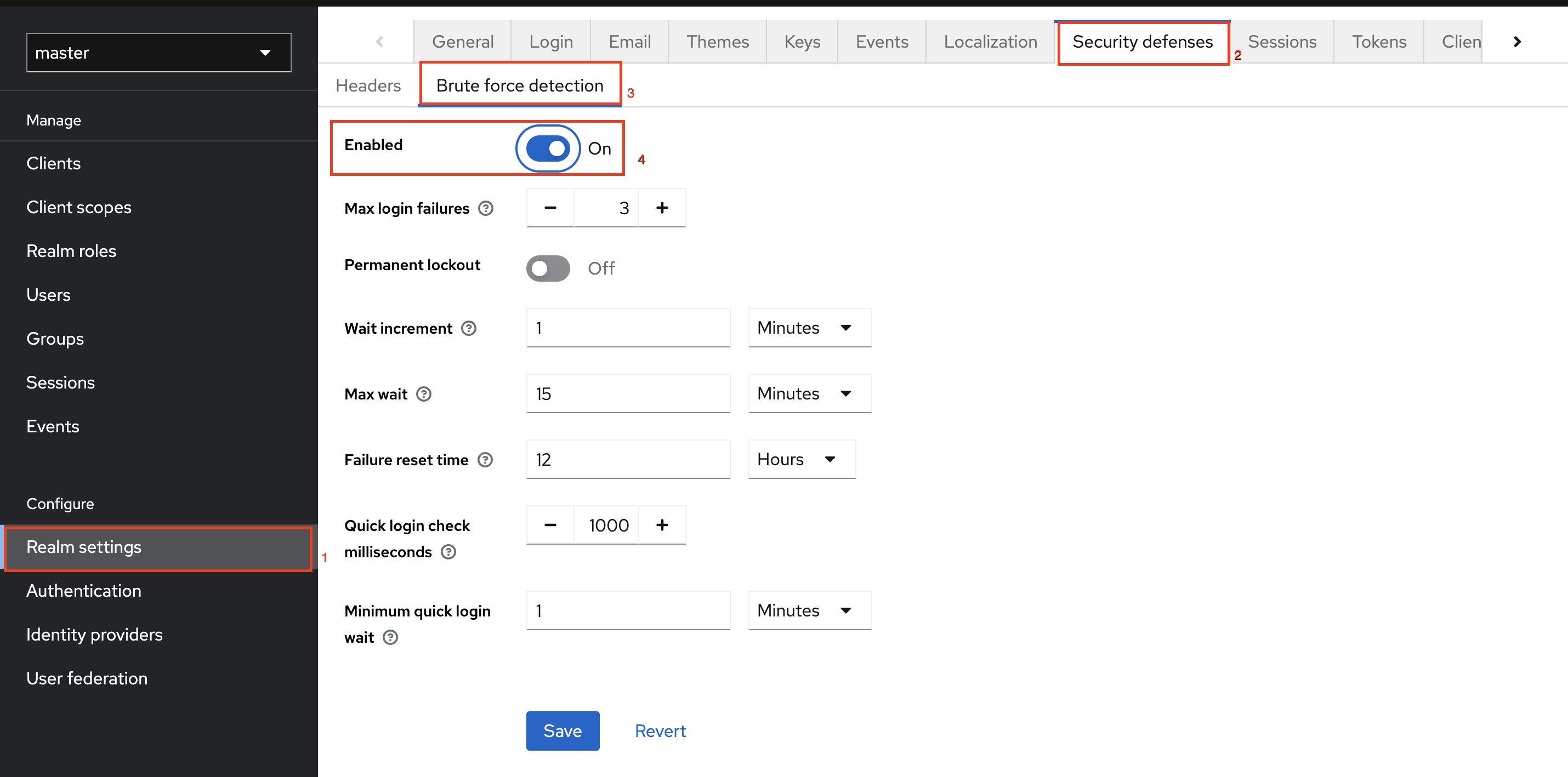
Parameters in Login Brute Force
Max Login Failures
| Name | Description | Default |
|---|---|---|
| Max login failures | A user can attempt to log in with incorrect credentials a maximum number of times before their account is temporarily locked. (For instance, if this value is set to 3, the user can make up to 3 incorrect login attempts. After three attempts, no further attempts will be allowed, and the account will be temporarily disabled.) | 3 failures |
| Permanent lockout | Login brute force protection triggers a permanent lockout that blocks a user's account permanently after a set number of failed login attempts. | |
| Quick login check milliseconds | The minimum amount of time that must pass between consecutive login attempts. This setting prevents BOT attacks and rapid login attempts. (For example, if set to 1000 milliseconds, the system will enforce a minimum delay of 1 second between login attempts. If attempts are made quicker than this, the account may be disabled.) | 1000 milliseconds |
| Minimum quick login wait | Temporarily disables a user's account for the minimum duration if they attempt to log in faster than the time specified in Quick login check milliseconds. (For example, if a user tries to log in multiple times within a few seconds, and this value is set to 1 minute, the user’s account will be disabled for at least 1 minute before they can try again.) | 1 minute |
Temporary Lockout Parameters
| Name | Description | Default |
|---|---|---|
| Wait increment | 1. The user is temporarily disabled when their login attempts exceed the Max Login Failures limit. 2. The wait time doubles with each additional attempt. (For instance, the lockout duration will increase from 2 minutes to 4 minutes after each subsequent failure if it is set to 2 minutes.) | 1 minute |
| Max wait | The maximum time a user will wait after failed login attempts. The wait time will not double beyond this limit. (For example, if set to 15 minutes, the system will lock the user's account for up to 15 minutes, after which the user can attempt to log in again.) | 15 minutes |
| Failure reset time | 1. The failure count resets to zero after a set period, starting from the last failed login attempt. It's important to set this value higher than the Max wait time. 2. No new failed login attempts should occur during this 12-hour period (For example, if the Failure Reset Time is set to 12 hours, the system will reset the failure count after 12 hours from the last failed attempt.) | 12 hours |
Mechanism of Wait Increment
For instance, if you have set Max login failures to 3 and a Wait Increment of 30 seconds, the effective time an account will be disabled after several failed authentication attempts will be,
| Number of Failures | Wait Increment (s) | Max Login Failures | Effective wait time (s) |
|---|---|---|---|
| 1 | 30 | 3 | 0 |
| 2 | 30 | 3 | 0 |
| 3 | 30 | 3 | 30 |
| 4 | 30 | 3 | 30 |
| 5 | 30 | 3 | 30 |
| 6 | 30 | 3 | 60 |
| 7 | 30 | 3 | 60 |
| 8 | 30 | 3 | 60 |
| 9 | 30 | 3 | 120 |
Note that after the 3rd failed attempt, the system disables the account for 30 seconds. The time increases from 30 to 60 seconds only when the number of failed attempts reaches the next multiple of Max Login Failures. The system extends the account lockout duration only at multiples of Max Login Failures. If the Effective Wait Time reaches the Failure Reset Time, the system resets the login attempt count.
Authenticators Incorporating Login Bruteforce
Certain authenticators incorporate Login Bruteforce protection within their flow,
- KOBIL Change Email - For more detailed information on the Brute force feature in the authenticator, please refer to KOBIL Change Email.
- KOBIL eTan - For more detailed information on the Brute force feature in the authenticator, please refer to KOBIL eTan.
- KOBIL Username Password Form - For more detailed information on the Brute force feature in the authenticator, please refer to KOBIL Username Password Form.
- KOBIL Delete Account - For more detailed information on the Brute force feature in the authenticator, please refer to KOBIL Delete Account.
- KOBIL Verify User Identity - For more detailed information on the Brute force feature in the authenticator, please refer to KOBIL Verify User Identity.
- KOBIL Email Registration, KOBIL Phone Registration, KOBIL Email Verification, KOBIL Phone Verification, and KOBIL CAPTCHA authenticators do not have specific brute force settings in their configuration tab. However, they come with default brute force protection enabled.
Execution summary
Login Brute Force Detection feature safeguards accounts by restricting the number of failed login attempts and enforcing lockouts. Key settings like Max login failures trigger lockouts after repeated failures, while Quick login check milliseconds prevents rapid retry attempts. The Failure reset time clears the failed attempt count after a specified period, offering a balance between security and user access, reducing the risk of brute-force attacks.